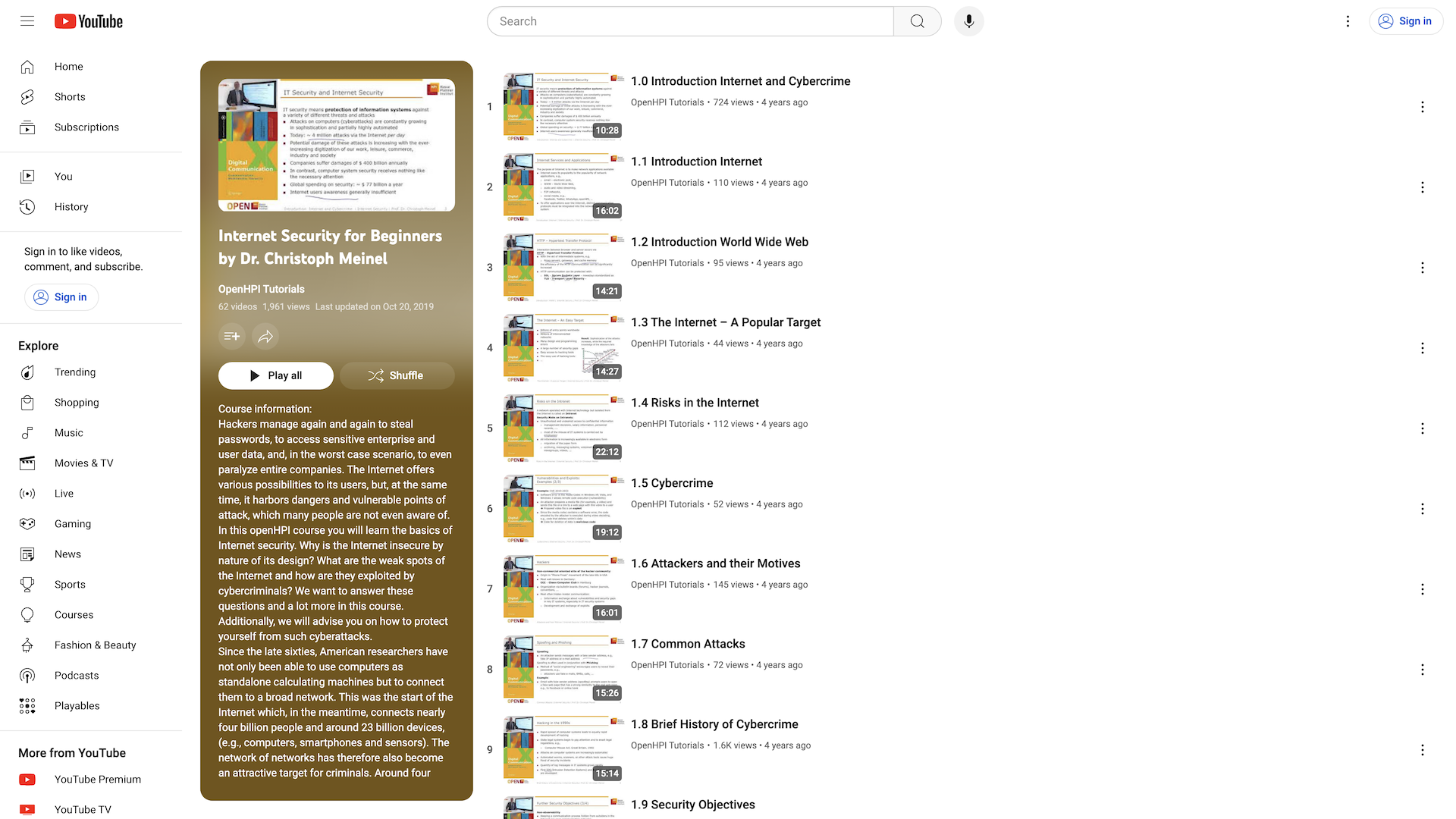
Internet Security for Beginners | Cybersecurity Fundamentals
Comprehensive introduction to internet security, covering threats, vulnerabilities, and defense mechanisms. Taught by leading expert Dr. Christoph Meinel.
Introduction
This course provides an introduction to internet security, covering the fundamentals of cybersecurity and how to protect oneself online. Taught by Dr. Christoph Meinel, a renowned expert in the field, the course is designed for beginners with no prior knowledge of internet security.
Highlights
- Comprehensive coverage of internet security basics, including threats, vulnerabilities, and defense mechanisms
- Practical tips and strategies for securing personal devices and online accounts
- Engaging video lectures and interactive exercises to reinforce learning
- Taught by a leading expert in the field of cybersecurity
Recommendation
This course is highly recommended for anyone looking to develop a strong foundation in internet security. Whether you're a student, working professional, or simply someone who wants to stay safe online, this course will equip you with the knowledge and skills to protect yourself and your digital assets.
YouTube Videos
How GetVM Works
Learn by Doing from Your Browser Sidebar

Access from Browser Sidebar
Simply install the browser extension and click to launch GetVM directly from your sidebar.

Select Your Playground
Choose your OS, IDE, or app from our playground library and launch it instantly.

Learn and Practice Side-by-Side
Practice within the VM while following tutorials or videos side-by-side. Save your work with Pro for easy continuity.
Explore Similar Hands-on Tutorials
Kubernetes Hardening Guidance
23Cryptography: Secure Communication & Data Protection
10Gray Hat Hacking: The Ethical Hackers Handbook
4Practical Cryptography for Developer
20Programming Differential Privacy
21The Joy of Cryptography (2021)
8Kali Linux 2018: Assuring Security by Penetration Testing, Fourth Edition
15Secure Programming HOWTO - Creating Secure Software
25Ethical Hacking | SQL Injection Attack Course
10Discover categories