Malware Dynamic Analysis | Open SecurityTraining Course
Dive into dynamic malware analysis, learn techniques for safe malware execution, and gain essential skills for effective malware investigation and mitigation.
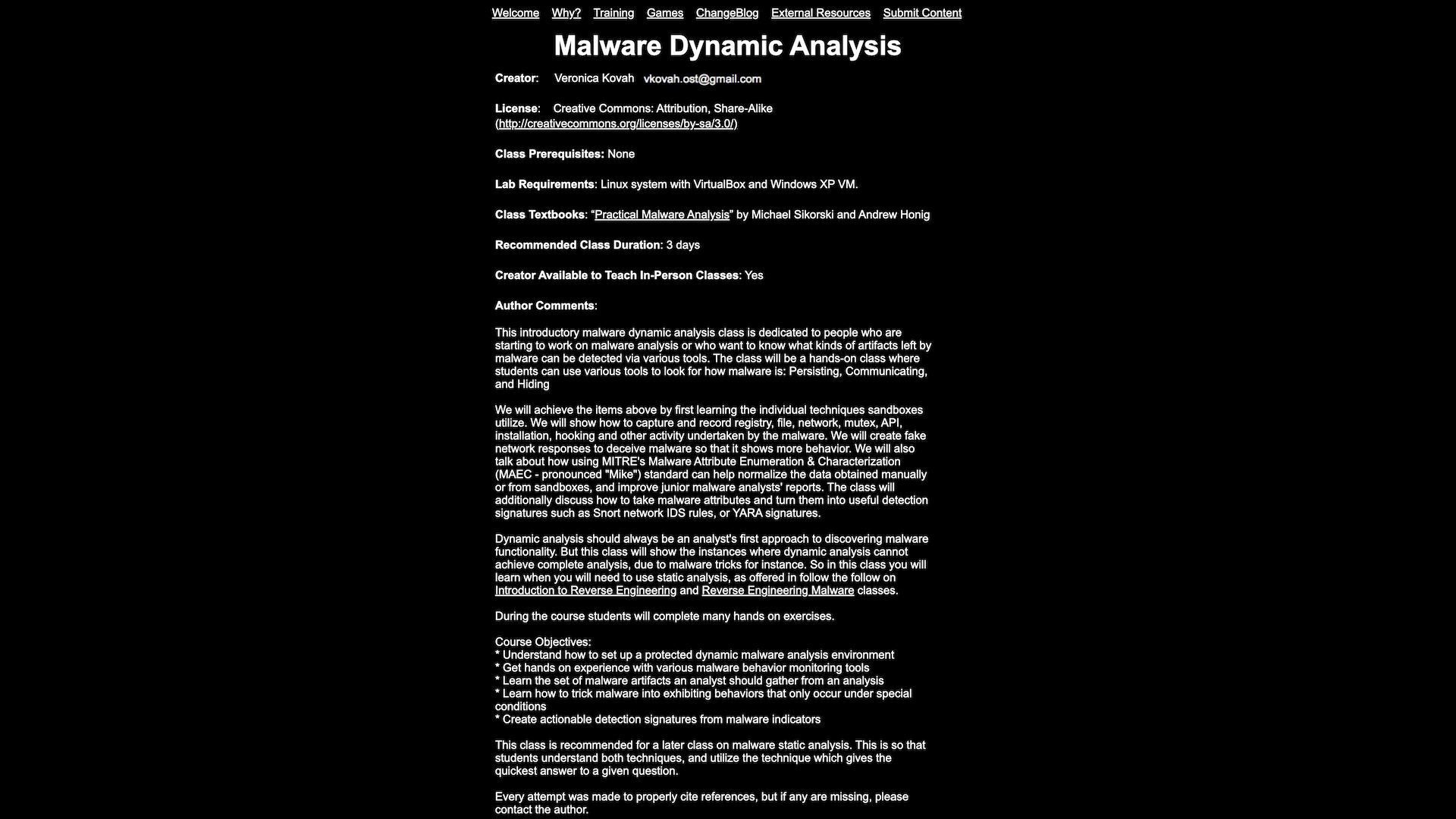
Introduction
This course provides an in-depth understanding of dynamic malware analysis, which involves executing and observing malware samples in a controlled environment to understand their behavior and impact.
Highlights
- Learn techniques for setting up a safe and effective malware analysis environment
- Explore methods for executing and monitoring malware samples to observe their behavior
- Gain skills in analyzing malware behavior, including network activity, file system changes, and process interactions
- Understand how to extract and analyze important artifacts from malware samples
- Discover tools and frameworks commonly used in dynamic malware analysis
Recommendation
This course is highly recommended for security professionals, incident responders, and researchers who need to analyze and understand the behavior of malware samples. It provides hands-on experience and practical skills that are essential for effective malware investigation and mitigation.
How GetVM Works
Learn by Doing from Your Browser Sidebar

Access from Browser Sidebar
Simply install the browser extension and click to launch GetVM directly from your sidebar.

Select Your Playground
Choose your OS, IDE, or app from our playground library and launch it instantly.

Learn and Practice Side-by-Side
Practice within the VM while following tutorials or videos side-by-side. Save your work with Pro for easy continuity.
Explore Similar Hands-on Tutorials
Kubernetes Hardening Guidance
23Cryptography: Secure Communication & Data Protection
10Gray Hat Hacking: The Ethical Hackers Handbook
4Practical Cryptography for Developer
20Programming Differential Privacy
21The Joy of Cryptography (2021)
8Kali Linux 2018: Assuring Security by Penetration Testing, Fourth Edition
15Secure Programming HOWTO - Creating Secure Software
25Ethical Hacking | SQL Injection Attack Course
10Discover categories