Computer Security | University of Illinois Urbana-Champaign
Develop the skills to build and manage secure systems with this comprehensive computer security course from the University of Illinois Urbana-Champaign.
Introduction
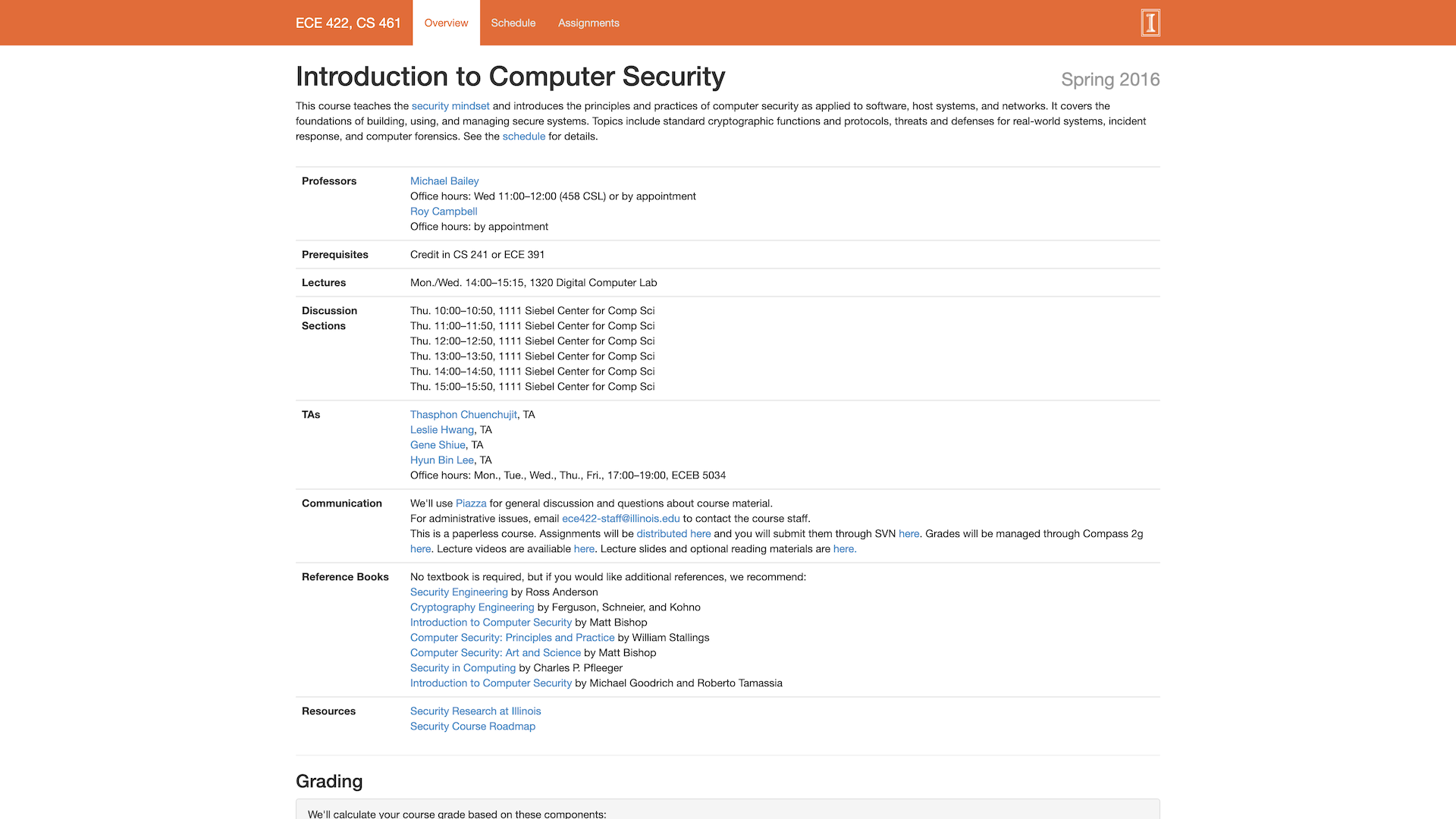
This course teaches the security mindset and introduces the principles and practices of computer security as applied to software, host systems, and networks. It covers the foundations of building, using, and managing secure systems. Topics include standard cryptographic functions and protocols, threats and defenses for real-world systems, incident response, and computer forensics.
Highlights
- Covers the security mindset and principles of computer security
- Focuses on building, using, and managing secure systems
- Includes topics such as cryptography, threats and defenses, incident response, and forensics
Recommendation
This course is recommended for students interested in computer security and who want to develop the skills to build and manage secure systems. It provides a strong foundation in the principles and practices of computer security.
How GetVM Works
Learn by Doing from Your Browser Sidebar

Access from Browser Sidebar
Simply install the browser extension and click to launch GetVM directly from your sidebar.

Select Your Playground
Choose your OS, IDE, or app from our playground library and launch it instantly.

Learn and Practice Side-by-Side
Practice within the VM while following tutorials or videos side-by-side. Save your work with Pro for easy continuity.
Explore Similar Hands-on Tutorials
Cryptography: Secure Communication & Data Protection
10Gray Hat Hacking: The Ethical Hackers Handbook
4Practical Cryptography for Developer
20Programming Differential Privacy
21The Joy of Cryptography (2021)
8Kali Linux 2018: Assuring Security by Penetration Testing, Fourth Edition
15Secure Programming HOWTO - Creating Secure Software
25Cracking Codes with Python
3Ethical Hacking | SQL Injection Attack Course
10Discover categories